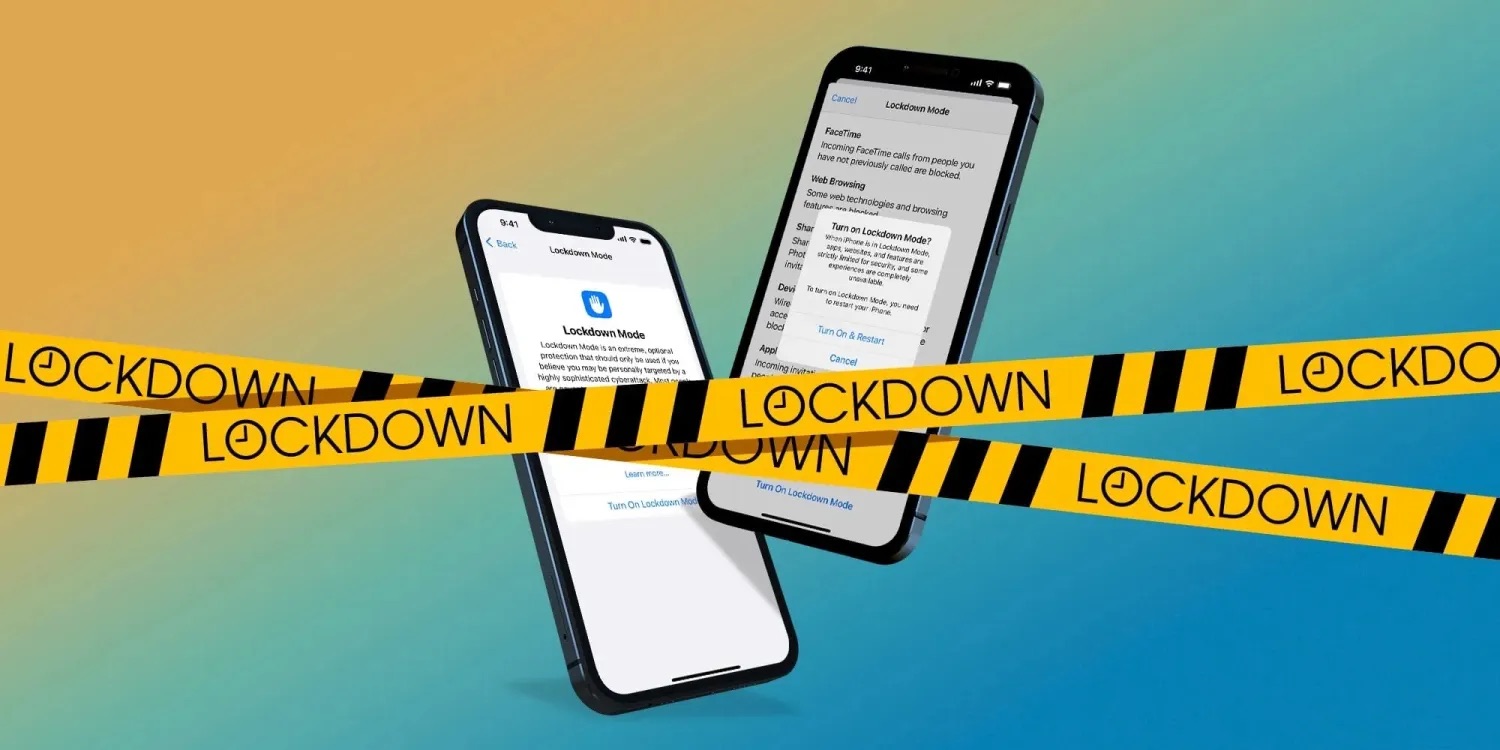
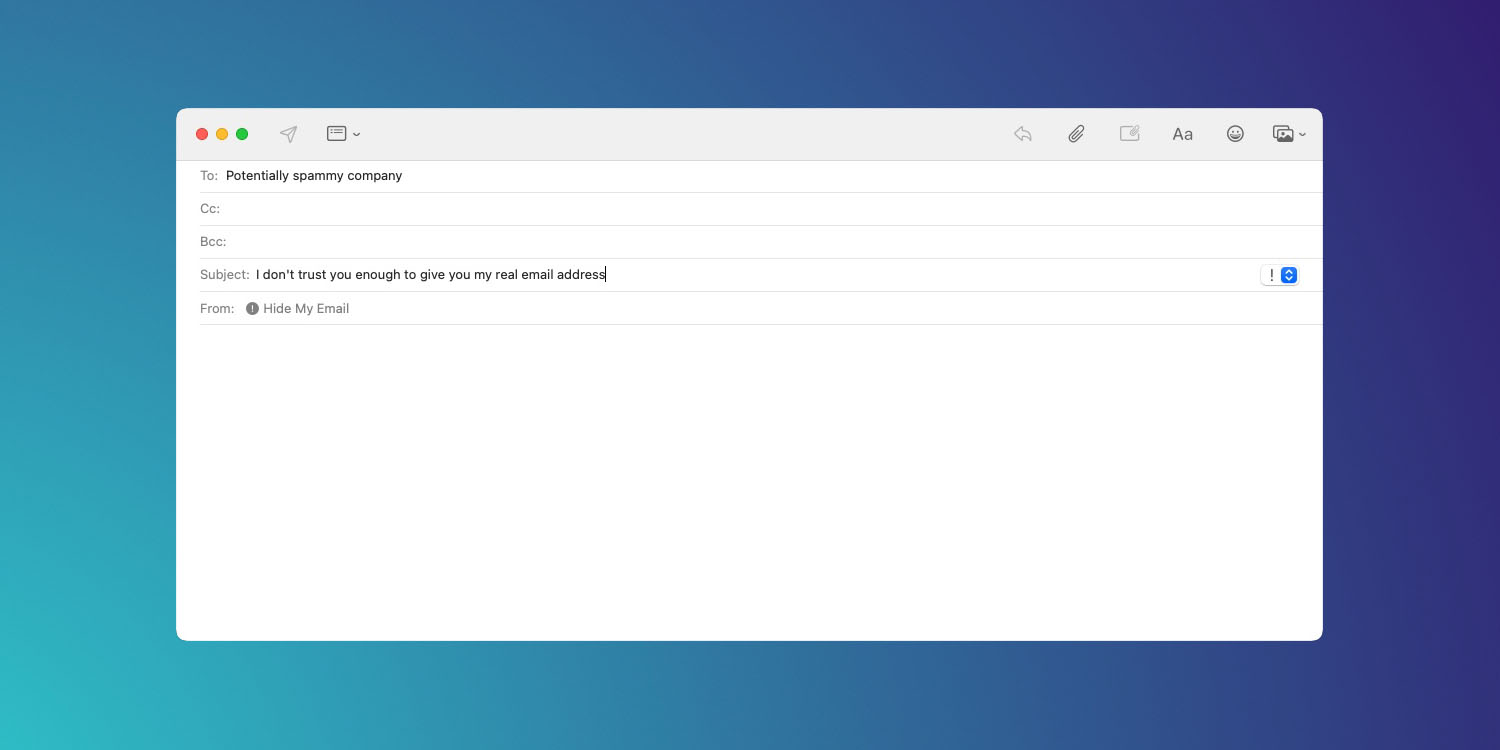
Privacy

Privacy is a growing concern in today’s world. Follow along with all our coverage related to privacy, security, what Apple and other companies are doing to keep your information safe, and what steps you can take to keep your information private.