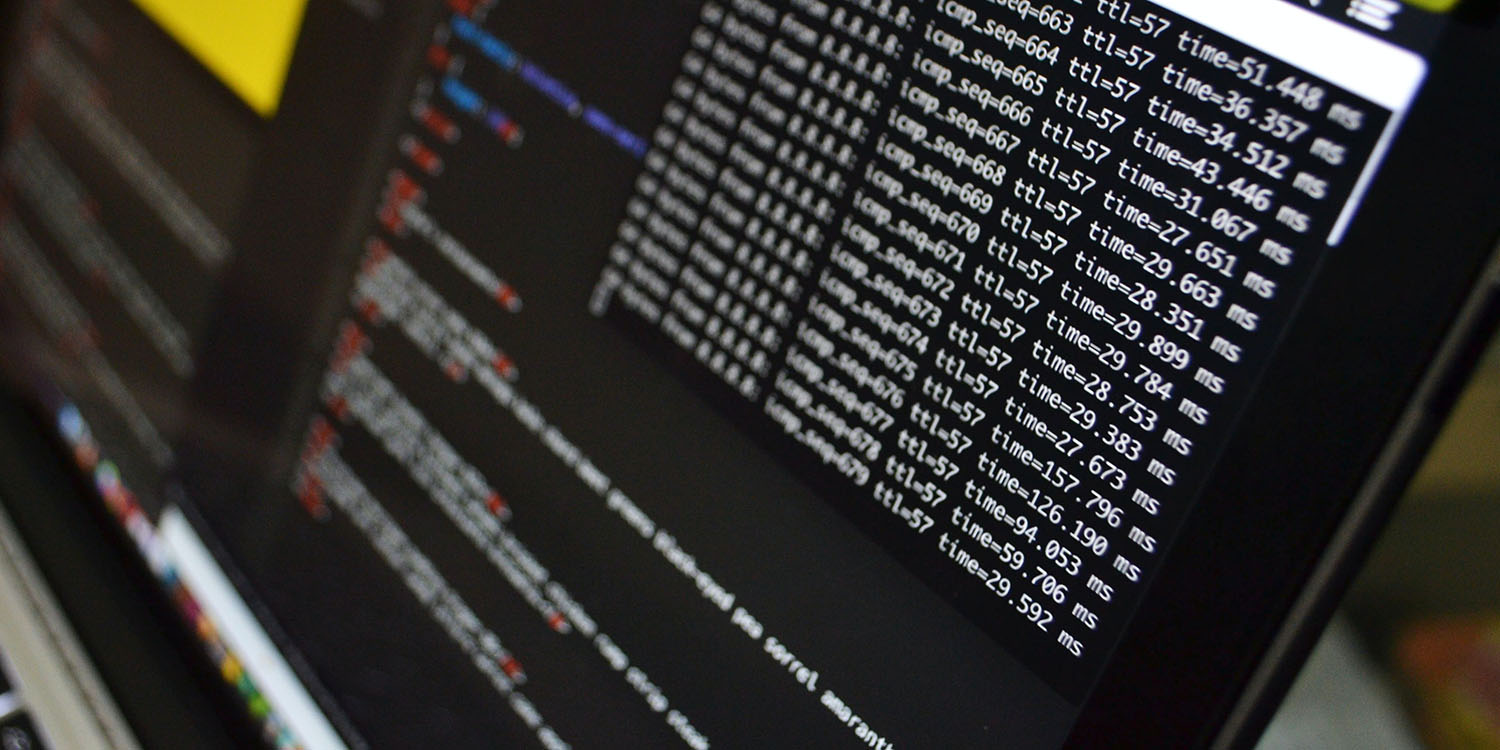
US Army iOS app among thousands that unknowingly used Russian code

A potentially sensitive US Army iOS app is among thousands of iOS and Android apps to include user-profiling code from a Russian company that pretended to be an American one – raising both privacy and security concerns.
The Centers for Disease Control and Prevention (CDC) also used the code in seven of its apps. Both organizations have now removed the code, but it remains present in thousands of other apps …
Expand Expanding Close